Facebook’s privacy and security missteps is nothing new.
Krebs on Security has pointed out a major bug in Facebook’s password management systems that caused hundreds of millions of users’ passwords to be stored as plaintext in an internal platform.
This means that thousands of Facebook employees could have searched for and found them. Though the report did not give out exact numbers of users whose passwords were exposed, it is estimated to be between 200 million and 600 million.

According to Wired, the inquiry revealed archives of user passwords in plain text which dated back to 2012.
However, Facebook denied in a blog post that the passwords were visible to anyone outside the company or abused or improperly accessed by its employees.
Our login systems are designed to mask passwords using techniques that make them unreadable. To be clear, these passwords were never visible to anyone outside of Facebook and we have found no evidence to date that anyone internally abused or improperly accessed them.
The issue was first flagged in January 2019 by the company’s security engineers, Facebook software engineer Scott Renfro.

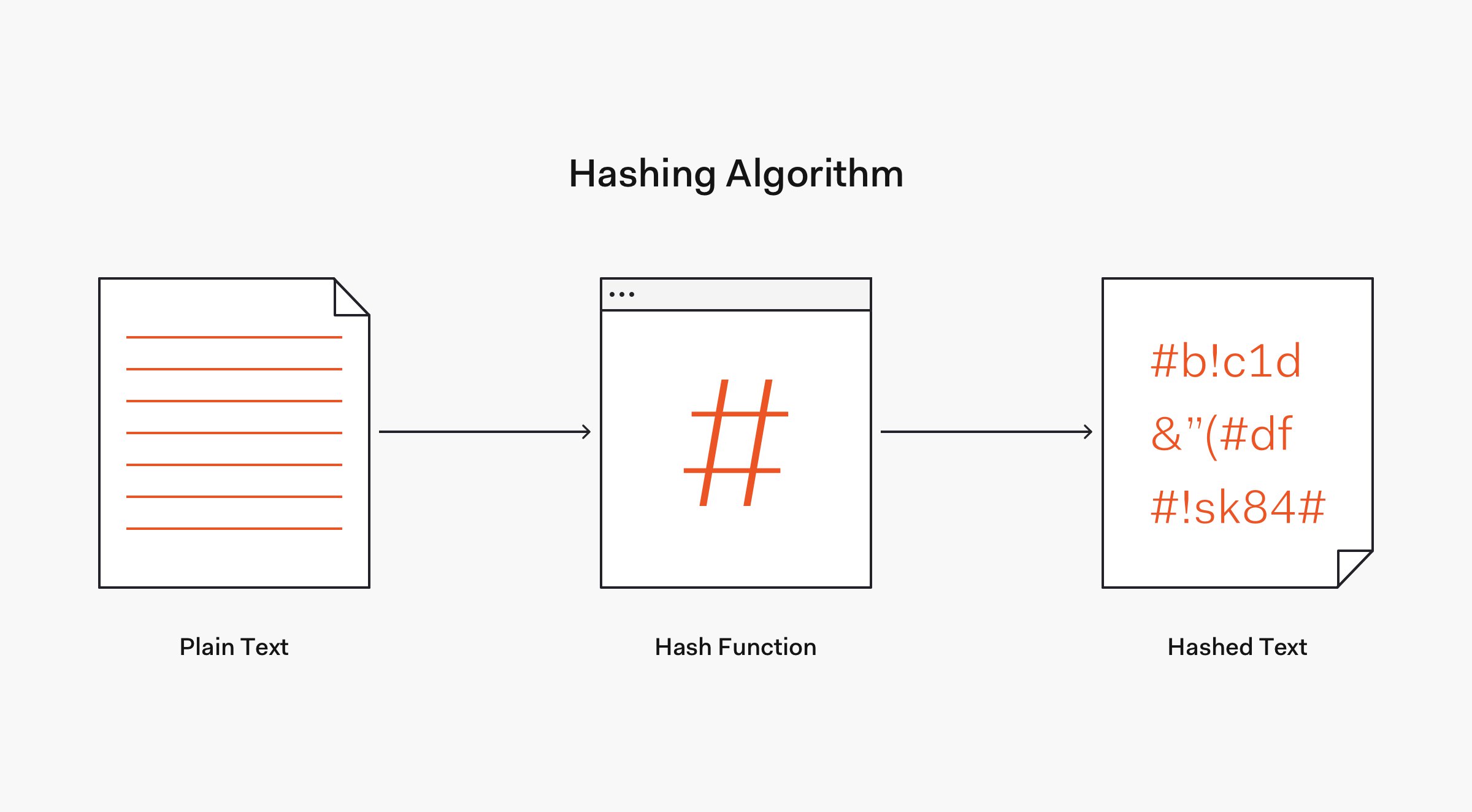
The norm for securely storing passwords is with a cryptographic process known as hashing.
This ensures that if someone compromises the passwords, they won’t be able to read them. Even a computer would find it difficult to unscramble them.
Facebook says that the plaintext password issue is now fixed, and that it doesn’t think there will be long-term impacts from the incident.